Cybersecurity trends and expected impact: Adapting to a remote world of work
Historically, cybersecurity initiatives focused on defensive measures inside the boundaries of traditional technology, such as company owned PCs/servers, etc. But today, policies like bring your own device (BYOD), growth of IoT, and remote work have blurred those lines and handed hackers a much broader realm to penetrate.
The importance of cybersecurity has been steadily increasing over the years to the point where executives outside of the IT department are taking notice and setting priority.
Cybersecurity can be categorized into five distinct types:
- Critical infrastructure security: Manage on-premise servers and storage, PCs, etc.
- Application security: Secure web or mobile applications
- Network security: Secure network within physical location as well as remote assets such as employee PCs and mobile devices
- Cloud security: Secure cloud infrastructure and data access control
- Internet of Things (IoT) security: Secure IoT devices that are deployed remotely and outside the typical bounds of infrastructure security
Priority of Cybersecurity Continues to Rise
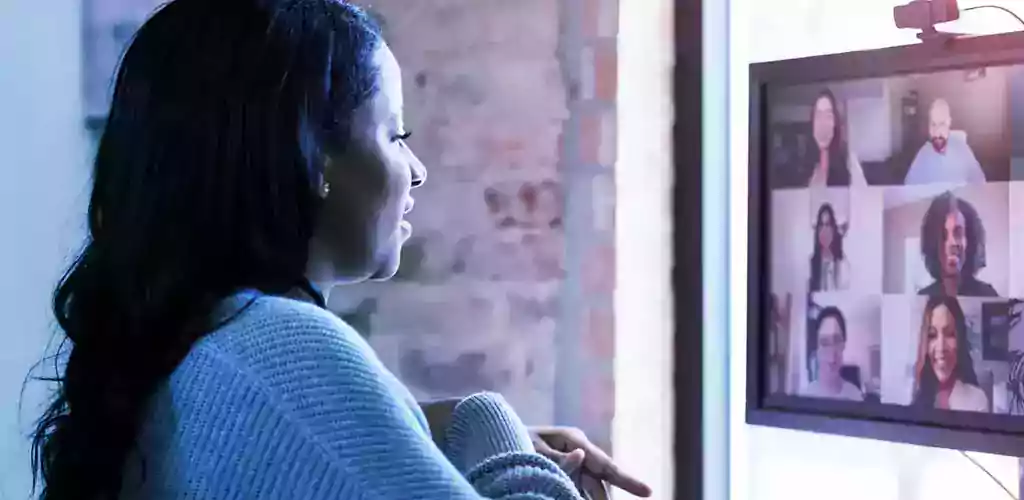
In 2022, undoubtedly, the biggest driver of change in cybersecurity has been the near immediate increase in remote working arrangements. The sudden relocation of much of the workforce to remote locations has created new areas of risk in application and network security realms.
According to Gartner, some of the key focus areas due to these new threats are:
- Incident response protocols and resources must be reviewed, updated, and tested to reflect the new working environment. If the organization does not have an incident response team, the organization should consider using the services of a managed security provider instead of standing up a new system.
- Secure and performance test all new entry points. Security teams should re-evaluate and possibly reinforce the level of security for corporate applications that store mission critical or personal information.
- Check that security monitoring tools and log management rule sets enable full visibility to cover the remote work paradigm. Ensure that MSPs are adopting the similar requirements if using one.
- Ensure foundational cybersecurity hygiene processes are in place while evaluating the prioritization of fixing security risks against the likelihood and impact of individual entry points.
- Artificial intelligence and machine learning will create opportunities. Investing in security process automation will increase the pace, accuracy, and scalability of performing security tasks, leaving more time to focus on more critical security functions.
- Artificial intelligence and machine learning will also create challenges. These technologies require security expertise to protect AI-powered digital business systems, leverage AI & ML to enhance security, and anticipate the use of malicious AI-based attacks.
References: Gartner, 7 security areas to focus on during COVID-19 Gartner, Top 9 security and risk trends for 2022
Icon cards headline here.
Card Two Title
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Integer nec odio. Praesent libero. Sed cursus ante dapibus diam. Sed nisi. Nulla quis sem at nibh elementum imperdiet uis sagittis.
Card Three Title
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Integer nec odio. Praesent libero. Sed cursus ante dapibus diam. Sed nisi. Nulla quis sem at nibh elementum imperdiet uis sagittis.
Card Three Title
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Integer nec odio. Praesent libero. Sed cursus ante dapibus diam. Sed nisi. Nulla quis sem at nibh elementum imperdiet uis sagittis.
“After witnessing two school systems that have successfully deployed a KES solution for their substitute staffing needs— along with the subsequent savings in hard and soft cost, time, and critical resources that our schools have realized— the question I typically ask any district on the fence is … ‘Who couldn’t afford to implement a KES program?’”
— Dr. Michael Henry, HR Director of Instructional Personnel, School District of Clay County
Related resources
We’ve got work figured out.
In calm or chaos, you can count on us for guidance. Because we’ve been around, and we’ll be here for you. We know a thing or two about the future of work—and we can’t wait to help you discover what’s next.
Contact us at 800.Kelly.01 and one of our agents will administer your request. Or, if you’d prefer, fill out the form to submit an email.
.svg)